Third party cloud security auditing firms engaged in the Federal Risk and Authorization Management Program (FedRAMP), are expressing concerns about significant new legal liability risks introduced by proposed changes to the FedRAMP process.
The concerns of the third party assessment organizations, known as 3PAOs, stem from draft guidance issued by the FedRAMP program management office that requires auditing firms to attest in writing to a cloud service provider’s readiness to enter the FedRAMP authorization process before formal testing is completed. The public comment period for the Draft Readiness Capabilities Assessment closes April 29.
“Several of the 3PAOs have commented that the wording of the attestation statement is problematic,” said Jeffrey Edelheit, director of Federal advisory services at KPMG, speaking Wednesday at the QTS IT Security & Compliance Forum in Washington, D.C. “The problem is that when the 3PAO then comes back and does the testing and says ‘oh, by the way, you’re not there,’ there are concerns that there could be significant legal ramifications to the 3PAO.”
The new documentation requirement is part of FedRAMP Accelerated, a new effort to revamp the Federal cloud security assessment process, which many have said takes too long, costs too much, and lacks transparency. But FedRAMP Director Matt Goodrich is standing firm on the new requirement.
“If we’re going to rely on our 3PAOs more heavily, I need a 3PAO to stand behind that readiness assessment. I need them to say ‘yes, I not only interviewed someone, I looked at evidence, I actually saw a demonstrated capability…I believe it’s true, and I’m putting my name behind it too,’ ” Goodrich said. “If a 3PAO can’t do that, then I don’t want to put much weight behind it.”
Goodrich said the attestation requirement at the beginning of the process does not pose any liability for 3PAOs because the attestation does not represent an authorization and, therefore, has no risk attached to it.
“I’m not asking for evidence…I’m not asking for a full assessment. I’m asking for a 3PAO to use their common sense knowledge and understanding of cybersecurity and how to investigate a system to tell if it is working or not,” he said.
But Goodrich had tougher words for auditing firms that might still be reluctant to sign the attestation.
“Frankly, the 3PAOs are more afraid of their CSPs than they are of FedRAMP right now,” said Goodrich. “They should be more afraid of the fact that if they don’t attest to something or stand behind the work that they’re doing, they’ll lose their accreditation and can no longer do that work. I want to rely on 3PAOs’ work more, which is what cloud providers want and what 3PAOs want. Well, then I need to be able to rely on that and 3PAOs need to put their word more heavily behind it. So trying to couch behind liability around something that there is no liability on doesn’t make sense to me.”
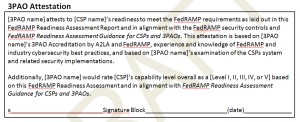 Draft FedRAMP Readiness Assessment Report.
Draft FedRAMP Readiness Assessment Report.
The goal under FedRAMP Accelerated is to achieve FedRAMP Ready status within 30 days, and a Provisional Authority to Operate (P-ATO) within three to six months.
The General Services Administration announced FedRAMP Accelerated just two months after a cloud industry advocacy group published a Fix FedRAMP position paper—a scathing assessment of the program’s shortcomings—and took their concerns to Capitol Hill, prompting lawmakers to promise closer oversight. GSA had refused to publicly comment on the paper by the FedRAMP Fast Forward Industry Advocacy Group and later pulled out of a meeting of the Cloud Computing Caucus Advisory Group on Capitol Hill.