Credit Monitoring
I would focus more on the M in CDM. We need to invest more horsepower into the mitigation and recovery. Think about it like this. An organization gets hacked and spills some PII. What does the agency do? The knee-jerk reaction will be to award a credit monitoring contract to support all the affected people. Last year OPM spilled a ton of information about me and tons of my peers in government. What did they do? They awarded a credit monitoring contract to help affected people recover.
So I am signing up for these credit monitoring services and I’m thinking to myself, “What am I actually signing up for? Is this service going to protect me from having bad guys open new lines of credit under my name? No. Is this service going to make me whole if bad guys actually open fraudulent lines of credit in my name? No. WFT am I actually signing up for?”
That’s my thought process. I’m thinking, what is the value of this activity? Here I am, giving a whole bunch more personal information to another organization [they will probably spill it too] and for what purpose? It is so funny when you think about it. Credit monitoring lets you know that you have been victimized faster. That is all it does. You will know faster that you have been victimized if someone opens a new line of credit that is reported to a credit reporting agency (Equifax, TransUnion, and Experian). That’s it.
It won’t notify you if someone files a fraudulent tax return in your name or tries to apply for Social Security benefits in your name. It won’t notify you if someone tries to access your health records at your hospital or from your insurance company. But people don’t think about all this other shit that could be affected, and probably about a thousand other things because your name, SSN, and birthdate have been compromised. But we like to think of credit monitoring as a prophylactic that insulates us from all this bad stuff, when really it just tells you that you have become a victim again.
In my opinion, credit monitoring is simply the lowest cost alternative for incident response. It doesn’t matter what the organization is, OPM, Target, Sony, VA, they spill your data, they are liable for their actions. Of the range of things they could do to restore your faith that they are taking the issue seriously, credit monitoring seems to be the lowest cost alternative that people will accept. We are like fucking lambs on this. We just accept that this is good enough and we are ignorant of the fact that it doesn’t do anything. I would argue that it is a fucking waste of money. Clearly I have strong feelings on this issue.
The problem is that hacking is on the rise, and not on a small build, but seems to be increasing at a significant rate. Add to that the innovation on the threat side and the different vectors they are using to gain access to organization data and the problem is increasing by an order of magnitude 3. I tell you this not to alarm you, this is just the simple truth. The issue is that the amount of data that is compromised as a result is also on the rise. I mean, the number of successful attacks is going to continue to increase. Our collective response to this is…credit fricking monitoring? We absolutely must do better.
But what would better look like? My answer to part of that is a Fraud Alert. Remember the law Congress passed that made it possible for every person to get a free credit report from one of the credit reporting agencies, the Fair and Accurate Credit Transactions (FACT) Act of 2003 4? Well, that law also created this thing called a “Fraud Alert,” which requires someone to really prove they are who they say they are, with a picture ID, before a new line of credit can be opened. Well that’s a pretty good idea. That would actually protect my credit much more than it is without it. Of course, there are limitations though. The Fraud Alert is only good for 90 days (it needs to be renewed), and a third–party firm, like a credit monitoring company, is prohibited from opening a Fraud Alert on your behalf.
Yeah, I about fell out of my chair when I learned this. First I was freaking shocked that there is actually something that could be done that would effectively insulate my credit from unauthorized entries. Second, of course, the thing that I receive no appreciable value from already is precluded from providing this service to me. I mean, how completely stupid is that, that we would not allow a credit monitoring company, paid to help people affected by a data breach, to enter a Fraud Alert on behalf of the people who opted in for their service?
You might ask how I know this. Because I have talked to companies that provide credit monitoring services and this is one of the services that they want to provide. I spoke with one company, who in fact was initiating Fraud Alerts on behalf of users who opted into their service. It wasn’t long before they received a cease and desist letter from Experian’s lawyers. See, Experian’s business is predicated on the fact that people should be able to open lines of credit quickly and easily. Anything that introduces friction into that process is considered bad and they fight that hard.
So when they sic their lawyers on a company they cite a case in California that never actually received a ruling, but included a stipulated order. The case is: Experian Information Solutions, Inc., a corporation, Paintiff, v. Lifelock, Inc., a corporation, Case No. SACV08-00165 AG(MLGx), Judge Andrew Guilford Feb. 13, 2008.
So you know me well enough by now. What are we, 100 pages in? It feels like 1,000 on account of my laziness. But my question is, how could Judge Guilford stipulate such a stupid decision that seems contrary to what people would want? Why would he side with the evil credit bureaus?
The Committee Report included the following very specific language that seems to be intended to keep these organizations from doing that.
| A request for a fraud alert must be made directly by the consumer, or directly by an individual acting on behalf of or as a personal representative of the consumer. The Committee used the word `individual’ instead of `person’ to ensure that the provision would only apply to specific individuals such as a consumer’s authorized family members or guardians (or attorneys acting as personal representatives), authorized representatives from bona fide military service organizations, and not to companies and entities such as credit repair clinics. |



 Sorry suckers!!!
Sorry suckers!!!
So I hope that somebody out there will pick up the torch for the common man and woman and propose a statutory change to fix this. The necessary fix is to allow credit monitoring companies to enter a “Fraud Alert” on behalf of the beneficiaries who opt-in to their service and to create an option for a “Fraud Alert” to have a one-year duration and be renewable annually. If we made this change then perhaps we could justify some of the expense for credit monitoring contracts.
The Calculus of a Breach
In thinking about a breach, not all breaches are created equal. There are some breaches in which hackers steal credit card numbers. That is actually one of the least impactful breaches. To recover from that, all you need to do is disable that credit card and have the company issue you a new one. Simple. But then there are breaches in which larger amounts of data are lost, Name + SSN + address + other stuff. These incidents have the potential to be much more impactful because bad people can use that information to do a whole lot more bad things.
All organizations and especially government agencies must recognize the responsibility that comes with collecting that information. I don’t think they generally take that responsibility seriously. We have a whole bunch of compliance activities that are supposed to help agencies take that seriously, but nobody ever thinks they will be hacked, or that they will be the ones who spill a person’s data. Everyone has a tendency to think that it will be those people over there, who aren’t diligent, and who don’t do a good job of securing their enterprise.
We have compliance tools like the Privacy Threshold Analysis (PTA), which helps you to understand if you need a Privacy Impact Assessment (PIA). Then after the PIA is done, you need to publish a System of Record Notice (SORN) in the Federal Register and get comments. I will submit that too frequently these steps are skipped, and that when they aren’t skipped, they aren’t done well or with the fidelity that is necessary. My opinion is that we need to think about this process, especially in the light of the mosaic effect.
The mosaic effect is the assembly of little bits of data to produce insights that weren’t possible when looking at the data in isolation. The earliest report I could find of mosaic effect concern was from 2004 5. To describe this, what if I could define a number of women in a neighborhood, say 200. Then separately, I could define the number of people who drive blue cars, say 100. Separate from both of those, I could define the number of people who wear blue sweaters, say 50. Eventually, if I add in enough data, I am talking about one single specific person, and I would know a lot about her.
Our tools for protecting privacy can’t account for this, and I would submit that there will never be a report or piece of paper that would help us to understand the extent to which we may be impacting an individual’s privacy. The PIA simply can’t figure this out. What we need is a system in which we can plug in the data we want to collect, and it will compare that data with the data that others have plugged in, and it will tell us the extent to which an individual’s privacy may be at risk.
But back to the calculus issue. There is a different impact based on the different amount of data lost.
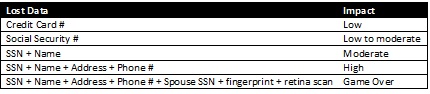
This idea is the concept behind Ericka Chichowski’s reporting on Black Market List Prices from the Dark Web 6. As you can see below, buying credentials with more information costs more on the black market.
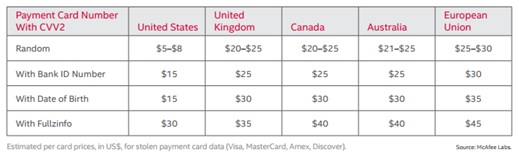 7
7
Once you start to get into things like fingerprints and retina scans, biometric data, guess what, you are compromised for life, unless you can figure out how to reset your fingerprint or the blood vessels in your eyes. But we pretty much treat every data breach the same. Our answer to all of these breaches is to go out and get credit monitoring. So you will get efficient access to your credit report for a year or two. Big deal.
But now add the mosaic effect to this. Maybe Target just lost my name and credit card. But then OPM lost a whole bunch of data about me. Someone else, who doesn’t even have the sophistication to know that they got hacked, like my eye doctor, loses my glaucoma test, the drug store loses the data about the prescriptions I’m taking. Pretty soon, bad people will know more about me than me.
Organizations (public and private) need to step up and start taking responsibility. The golden rule here is, if you don’t have the capacity to protect the confidentiality, integrity, and availability of the data, then you shouldn’t have the right to collect it in the first place.