Cyber criminals are more and more often using tools and processes already installed in target computers, called “living off the land,” to ease hacking efforts and reduce the chance of detection, according to a recent Symantec study. […]
The White House is celebrating Made in America Week, while many U.S.-based technology companies advocate for H-1B visas to sponsor foreign workers who engineer some of the nation’s most lucrative technology products. […]
The Federal Acquisition Regulation, the guidelines dictating how Federal agencies procure goods and services, is not flexible enough to keep pace with modernizing agencies, according to Jennifer Hoover, DevOps program manager for the Transportation Security Administration. […]
The Department of Homeland Security Science and Technology Directorate is hosting its 2017 Cyber Security Research and Development Showcase featuring more than 115 technologies. The showcase, the Federal government’s largest cybersecurity training workshop, will run July 11-13 at the Mayflower Hotel in Washington, D.C. […]
As the needs of Federal employees push agencies to move more and more services to the cloud, join MeriTalk and Government Acquisitions Inc. for the Federal Focus: The Cloud Generation event on July 12 at the Newseum in Washington, D.C., to discuss the best practices and results of Federal cloud migration. Rep. Gerry Connolly, D-Va., co-author of FITARA and IT reform advocate, will keynote the lunch session at the event. […]
Some states refused to turn over voter data to the White House on June 30, saying that the data requested contains sensitive information and could be used for political purposes. President Donald Trump signed an executive order in May that established the Commission on Election Integrity, which investigates instances of potential voter fraud. The commission asked the states to turn over all publicly available voter data. […]
Representatives of the intelligence community said that they want the surveillance powers outlined in the Foreign Intelligence Surveillance Act (FISA) to be renewed without amendment or sunset clause this year. […]
To protect the nation’s digital infrastructure, Rep. Will Hurd, R-Texas, said it’s important to empower agency leadership and expand information sharing between the Federal government and other entities. […]
Congress will be busy with future tech initiatives and members have high hopes for the potential of current programs, according to two congressmen who spoke June 7 at MeriTalk’s Cloud Computing Brainstorm. Congressional IT leaders Reps. Will Hurd, R-Texas, and Gerry Connolly, D-Va., talked about the future of major IT initiatives such as FedRAMP, the Modernizing Government Technology (MGT) Act, FITARA, and executive leadership, offering insight into the shape of IT developments in the coming months. […]
Darron Makrokanis, vice president of Federal for Tenable Network Security, said the cybersecurity executive order’s time frames are a “bit aggressive,” but the emphasis on cybersecurity is a step in the right direction. Makrokanis will be speaking at Tenable’s GovProtect discussion on June 21. […]
Congress’ power of the purse, enunciated in Article I of the Constitution, is at the very heart of its authority and role in our democracy. That’s why I’m somewhat amused by all the concern, gnashing of teeth, press articles, and the like about President Trump’s recent release of his FY 2018 budget. […]
A broad range of experts in FedRAMP, Cloud, and IT Modernization will gather at the Newseum in Washington, D.C., on June 7 to discuss the future of cloud acquisition in the Federal government. MeriTalk’s “The Modernization Movement: Cloud for Next-Gen Government” event will take an in-depth look at the trajectory of Federal cloud acquisition and what it means for government and industry. […]
The deadline for Federal contractors to complete insider threat training programs under a Department of Defense rule change arrives on May 31, and Bay Dynamics Federal Systems Engineer Thomas Jones calls the mandate an “excellent first step” in improving protections against insider threats. […]
The Congressional Budget Office released its updated score for Rep. Will Hurd’s Modernizing Government Technology Act, placing the bill’s cost at $500 million over five years, down from the $9 billion estimate placed on the last version of the bill. […]
The U.S. government workforce is not prepared to deal with the kind of information warfare that Russia used to influence the 2016 presidential election and has continued to use in the elections of other nations, U.S. Cyber Command and NSA Chief Admiral Michael Rogers told members of the Senate Armed Services Committee. […]
The IT professionals at the Department of Defense are learning to speak the language of the warfighter. […]
The Government Accountability Office issued a report that said that 26 agency inspectors general reported that their agencies faced challenges in meeting the deadline for DATA Act required information. […]
For IT acquisitions professionals in the Department of Defense, Buy American provisions can do far more harm than good, according to former DoD officials testifying in front of the House Armed Services Committee. […]
Technology developers and government agencies know how to incorporate cybersecurity into their products, but the question is whether they have the will to do it, according to National Institute of Standards and Technology fellow Ron Ross. […]
The Department of Labor gave the NOVA Workforce Board $1,660,430 to continue its effort to provide re-employment and training services to workers affected by layoffs and closures at 70 companies in Silicon Valley. […]
Following the release of Office of Management and Budget’s plan to restructure the executive branch, agencies have begun to discuss plans to eliminate unnecessary regulations and reduce their workforces. Here’s the rundown by agency. […]
The government doesn’t need “nongovernment culture” to improve cybersecurity. What it needs is to recruit a workforce with a long-term vision of service and innovators driven not by the prospect of living a life of success but of living a life of meaning. Nowhere is this more apparent than at NASA. […]
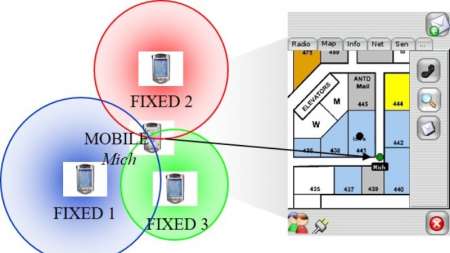
A National Institute of Standards and Technology (NIST) research team collected data from four different smartphone models over an 18-month period to further the development of indoor navigation apps. This type of technology would assist users in finding their way inside unfamiliar buildings, help emergency responders find victims, direct visitors to find specific works of art in large museums, and more. […]
The foreign ministers of the G7 nations expressed increased concern about cyber interference in elections. Leading up to the G7 Summit in Italy in May, they also adopted the G7 Declaration on Responsible States Behavior in Cyberspace. […]
The Federal Trade Commission announced that it charged Sentinel Labs, SpyChatter, and Vir2us with violating privacy agreements with countries in Asia. […]
MeriTalk reporters and editors were awarded a first place (gold) and two second place (silver) regional awards for excellence by the American Society of Business Press Editors. […]
As the State Department works to gain international support for its cybersecurity framework, experts said that global norms and deterrence won’t be enough to convince state actors not to influence elections through cyber means in the future. […]
The IT community needs a total reset in the way they think about cybersecurity, according to former White House CIO Theresa Payton. […]
A military-funded technology that can influence the emotional centers in a person’s brain is ready to receive its first human test subjects. The device, a deep brain stimulator, was created as part of the Department of Defense’s Systems-Based Neurotechnology for Emerging Therapies (SUBNETS) program. […]
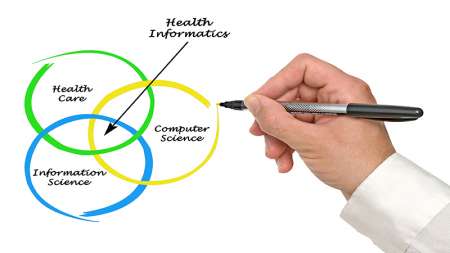
A truly stunning detail overlooked by most observers during the confirmation process of David Shulkin to become secretary of Veterans Affairs is that the VA is going to hire a chief health informatics officer to lead the agency’s electronic health record strategy. […]